Millions Stolen: FBI Investigation Into Office365 Executive Account Breaches
Table of Contents
The Scale of the Office365 Executive Account Breach Problem
The problem of Office365 executive compromise is far-reaching and deeply concerning. While precise figures from the FBI investigation may not yet be publicly available, anecdotal evidence and industry reports suggest a substantial number of organizations and individuals have been affected.
Number of affected organizations and individuals
Unfortunately, comprehensive statistics on the exact number of affected organizations and individuals remain largely undisclosed due to the ongoing nature of the FBI investigation and the sensitive nature of the data involved. However, cybersecurity firms consistently report a rise in targeted attacks against high-profile individuals within organizations.
- Industries Most Targeted: The finance, technology, and healthcare sectors are particularly vulnerable due to the sensitive data they handle and the high value placed on their intellectual property. Government agencies are also frequently targeted.
- Types of Data Compromised: Breaches often result in the theft of highly sensitive information, including financial records, intellectual property, strategic plans, sensitive employee data (including personally identifiable information or PII), and customer data.
- Financial and Reputational Consequences: The repercussions extend far beyond the immediate financial losses. Businesses face significant reputational damage, loss of customer trust, legal ramifications, and the substantial costs associated with remediation and recovery efforts. The impact of high-level Office365 account breaches can cripple an organization for months or even years.
FBI Investigation Tactics and Findings (if publicly available)
While details surrounding the FBI's investigation into Office365 executive account breaches are often kept confidential for ongoing investigative reasons, publicly available information can shed light on common attack vectors.
Methods used by the attackers
Attackers employ a range of sophisticated techniques to gain access to executive-level Office365 accounts.
- Phishing: This remains a highly effective method, often utilizing carefully crafted emails designed to trick executives into revealing their credentials.
- Credential Stuffing: Attackers use stolen credentials from other breaches to attempt access to Office365 accounts.
- Exploiting Vulnerabilities: They may exploit known vulnerabilities in software or configurations to gain unauthorized access.
Specific details about the FBI's investigation, arrests made, or indictments, are generally not released to the public until the investigation concludes. This is to protect the integrity of the investigation and to avoid alerting potential suspects. However, information regarding the types of malware or ransomware used, and attacker motives, might become public as the investigation progresses. These motives can range from financial gain to espionage or corporate sabotage.
Protecting Your Organization from Office365 Executive Account Breaches
Proactive security measures are critical to preventing Office365 executive account breaches.
Implementing robust security measures
A multi-layered approach is necessary to effectively protect against these targeted attacks.
- Multi-factor authentication (MFA): Implement MFA for all accounts, especially those with executive-level access. This adds an extra layer of security, making it significantly harder for attackers to gain access even if they obtain passwords.
- Security Awareness Training: Regularly conduct comprehensive security awareness training for all employees, focusing on identifying and avoiding phishing attempts and other social engineering tactics.
- Strong Password Policies: Enforce strong password policies and consider using a password management tool to help manage and secure passwords.
- Regular Security Audits and Vulnerability Assessments: Conduct regular security audits and penetration testing to identify and address vulnerabilities in your systems and applications.
- Incident Response Planning: Develop and regularly test a comprehensive incident response plan to ensure a swift and effective response in the event of a breach. This includes clearly defined roles and responsibilities, communication protocols, and recovery procedures.
The Long-Term Impact and Implications of Office365 Executive Account Breaches
The consequences of Office365 executive account hacking extend far beyond the immediate loss of data.
Long-term effects on businesses and individuals
- Reputational Damage: A data breach can severely damage an organization's reputation, leading to loss of customer trust and impacting its ability to attract investors.
- Legal and Regulatory Consequences: Organizations may face hefty fines under regulations like GDPR for failing to adequately protect sensitive data.
- Ongoing Costs of Remediation and Recovery: The process of recovering from a breach, including forensic investigation, data recovery, legal fees, and notification costs, can be extremely expensive and time-consuming.
- Potential for Long-Term Financial Losses: The long-term financial impact of a breach can be substantial, affecting revenue, market share, and overall business value.
Conclusion
The FBI's investigation into Office365 executive account breaches underscores the critical need for robust security measures. The scale of the problem, coupled with the potentially devastating consequences, necessitates a proactive and multifaceted approach to security. By implementing multi-factor authentication, conducting regular security awareness training, enforcing strong password policies, and establishing a comprehensive incident response plan, organizations can significantly reduce their risk of experiencing costly and damaging Office365 executive account breaches. Protect your organization from costly Office365 executive account breaches by implementing robust security measures today! Learn more about securing your Office365 executive accounts and mitigating the risk of data breaches by researching best practices and consulting with cybersecurity professionals.
Featured Posts
-
 Exploring Agatha Christies Poirot His Cases Character And Enduring Legacy
May 20, 2025
Exploring Agatha Christies Poirot His Cases Character And Enduring Legacy
May 20, 2025 -
 Reddits Top Picks 12 Promising Ai Stocks For 2024
May 20, 2025
Reddits Top Picks 12 Promising Ai Stocks For 2024
May 20, 2025 -
 Nouvel Espace Restauration Galeries Lafayette Biarritz Soiree Speciale Avec Imanol Harinordoquy Et Jean Michel Suhubiette
May 20, 2025
Nouvel Espace Restauration Galeries Lafayette Biarritz Soiree Speciale Avec Imanol Harinordoquy Et Jean Michel Suhubiette
May 20, 2025 -
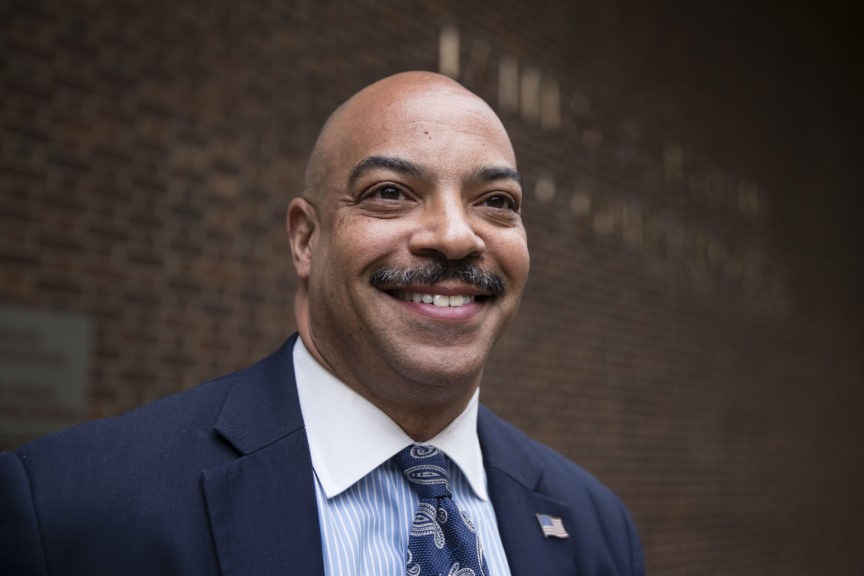 Admirals Bribery Trial Defendants Claim Case Reveals Systemic Navy Issues
May 20, 2025
Admirals Bribery Trial Defendants Claim Case Reveals Systemic Navy Issues
May 20, 2025 -
 Michael Schumacher Grand Pere Pour La Premiere Fois D Une Petite Fille
May 20, 2025
Michael Schumacher Grand Pere Pour La Premiere Fois D Une Petite Fille
May 20, 2025
Latest Posts
-
 A Hell Of A Run Ftv Lives Impact On Broadcast Journalism
May 20, 2025
A Hell Of A Run Ftv Lives Impact On Broadcast Journalism
May 20, 2025 -
 Mainz 05 Vs Leverkusen Full Match Report And Highlights From Matchday 34
May 20, 2025
Mainz 05 Vs Leverkusen Full Match Report And Highlights From Matchday 34
May 20, 2025 -
 Fsv Mainz 05 Vs Bayer 04 Leverkusen Matchday 34 Report And Highlights
May 20, 2025
Fsv Mainz 05 Vs Bayer 04 Leverkusen Matchday 34 Report And Highlights
May 20, 2025 -
 Mainz Defeat Rb Leipzig Thanks To Burkardt And Amiris Heroics
May 20, 2025
Mainz Defeat Rb Leipzig Thanks To Burkardt And Amiris Heroics
May 20, 2025 -
 Burkardt And Amiri Power Mainz To Victory Over Leipzig
May 20, 2025
Burkardt And Amiri Power Mainz To Victory Over Leipzig
May 20, 2025
